Organizations are now facing unprecedented threats that come from a global network of ransomware attackers and cybercriminals. From the Colonial Pipeline to your local hospital, every day there are outages and ransom payments that have escalated ransomware protection as a top initiative for most infosec professionals. Like any other infosec challenge, protecting your organization’s data from ransomware attacks requires constant vigilance as attackers develop ever more sophisticated attacks. For our customers, VAST is quickly becoming the destination for the digital assets of an enterprise, and we want to do our part in helping organizations protect these assets from cybercriminals.
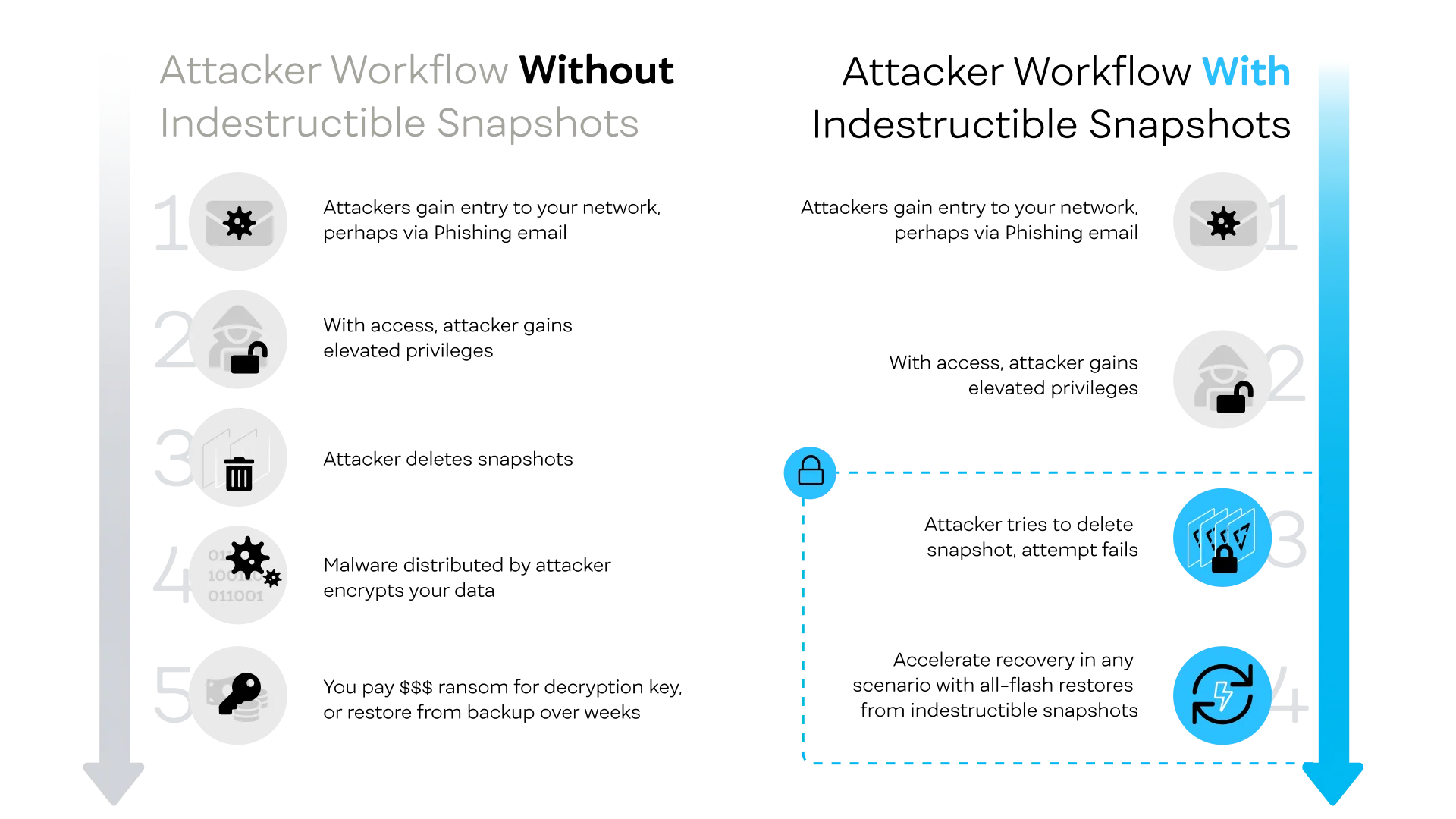
Enterprise storage systems have long been a backstop against a ransomware breach, when read-only snapshots are enabled. By virtue of them being read-only, snapshots become immutable objects that ransomware attackers cannot encrypt and hold for ransom. While immutable snapshots are a good primary line of defense against crude viruses that are self-executed within an organization’s network - more sophisticated attacks will involve human’s first penetrating a network through the use of malware and/or phishing, and then gaining access to storage system settings and/or APIs in an attempt to delete snapshots and snapshot policies just before primary data is crypto-locked. When snapshots are our primary line of ransomware defense, we become defenseless when they are deleted.
Today, we’re happy to announce a new feature coming to v4 of VASTOS that we call Indestructible Snapshots. This new feature provides an additional layer of protection that safeguards your immutable snapshots from sophisticated external attacks (or even rogue employees) by preventing any individual from deleting indestructible snapshots before their expiration date.
WORM vs SC-WORM
The VAST Data Platform was designed to power tomorrow’s generation of dynamic applications. VAST engineered the architecture for more than just compliance archives, where customer directories and buckets can be written to by researchers, artists and data scientists in ways that are at times unpredictable. This power and flexibility works against the original design point for enterprise WORM (write-once, read-many) storage systems. Enterprise WORM products, such as systems that comply with the SEC’s 17a-4 regulation, make it impossible to overwrite, tamper or delete data once it’s written.
While WORM is an essential feature to support government oversight, WORM principles can also be too inflexible for customers who are simply attempting to protect themselves from cybercriminals. In a dynamic application environment, WORM locks can create a potentially dangerous situation where one run-away application or user creates too much (immutable) data that fills a storage system. In this case, the natural recourse would be to delete that data or its snapshot, but with WORM snapshots enabled the snapshot would not be able to be deleted until the WORM policy expires. There are also other cases for WORM snapshots to be changed…for example, when an administrator accidentally snapshots data too frequently or creates a policy with an unnecessarily long expiration period.
To balance the needs of modern infosec and dynamic computing and administration environments, a smarter and more flexible approach is required to protect storage snapshots. This is why we are introducing the concept of “Securely Changeable” WORM snaps. Here’s how it works:
Making Snapshots Indestructible
To make snapshots indestructible, select the “Indestructible” option when creating a protection policy. Since indestructible snapshots are immutable until their expiration date, these snapshot policies must also specify a finite retention period.
Any data written under the Indestructible policy will be immutable until its expiration date. To make data truly indestructible we also prevent a rogue administrator from playing the long game. Admins will not be able to reset a policy to remove the indestructible flag and wait until the indestructible snaps expire before deleting user data. Not only are the snapshots indestructible, but the policies themselves are also indestructible and cannot be tampered with.
In the case where a policy was set incorrectly or when a user has unexpectedly over-run the system with data, an organization may really need to delete an Indestructible Snapshot. In this case, VAST customers can follow a pre-established protocol where one (or two) customer administrators can contact VAST Support to receive a deletion token that enables an Indestructible Snapshot to be deleted. By requiring two customer administrators to authenticate with VAST Support, this process is not dissimilar to a nuclear weapon launch sequence where multiple keys are required to detonate a snapshot. The process of authorization includes a challenge-response pass phrase that is specific to each administrator so only someone who knows how to respond to “What is the flight speed of an unladen swallow?” (“African or European?”, of course) can be authorized to receive a time-based key from VAST’s support team. These tokens are cryptographically generated uniquely for each cluster and are only valid for a limited period, again to protect against a rogue admin convincing management to get them the deletion token and then destroying data weeks or months later.
So there you have it. Indestructible Snapshots provide customers with the assurance that their snapshots will be immutable, while also providing a multi-factor mechanism that enables only authenticated customers to get themselves out of a jam should they mistakenly fill their system to the brim. Indestructible snapshots are just the first in a series of ransomware protections that we have planned for the VAST Data. We’ll update on this more as these additional features become available.
If you want to learn more about Indestructible Snapshots, contact us today.



